by hash3liZer . 09 September 2019
WPA/WPA2 cracking has been a focus point in the community since many years. And we have tools to aim that focus like aircrack and hashcat. Some new advancements have been made to aid that focus in the past couple of years.
GPU memory access requires to be done on 128bits or more for best performance and if possible all memory access shall be avoided. GPU shall use as most as possible registers instead of shared memory. Lot of other hints to found specific to each constraint. Change Log GPUmd5crack v0.2.3 changes. Multiple computing cores were made up of multi-core CPU and GPU on single PC to crack in parallel. GPU contributed to the cracking speed improvement due to the strong computing power for intensive.
So, Cracking WPA/WPA2 has been quite a topic now. In this tutorial, we are going to cover one of the infamous tools 'hashcat' for cracking WPA/WPA2.
Hashcat which is primarily built for brute forcing different kind of hashes using different kind of attack vectors, supports cracking for two of badly known WPA/WPA2 attacks. Well, for the list of available hashes, you can check the hash modes section in the manual:
In previous, you might have seen or even worked with aircrack to crack WPA/WPA2 by capturing a 4-way handshake. But that was not anywhere close to how perfect could this tool be for the purpose. Easefab video converter registration code. Besides, hashcat is a GPU + CPU maintained tool which makes it a lot more faster.
In short, if you own a GPU, always go for hashcat or else you could use an online service or buy out some GPU based server on Internet.
We will cover up with two famous WPA/WPA attacks, precisely the cracking of MIC (4-way handshake) and PMKID (1st packet/handshake). So, let's begin.
Installation
Hashcat is built to work on Windows, Linux and as well as on Mac. You can go to hashcat.net and download the binaries and follow the instruction for your operating system. What we are going to do here is clone a fresh copy of hashcat from github and manually install it on a debain based linux.
Preferably, you should use Kali Or Parrot but a similar distro like Ubuntu will work as well.
Update Your Repo's and install the following dependencies:
Clone hashcat from github and move to directory:
Finally, compile the binaries and we are all set with hashcat.
You may try printing the help manual for hashcat to check whether you have it installed perfectly or not.
Hcxtools:
Now, let's clone and compile hcxtools from github. It is basically a set of various files to convert and generate another version of the supplied input. We will use it to convert the captured traffic into a format understandable by hashcat. Celeste ost golden.
First, clone the repo and move the hcxtools directory:
And finally, run the make command to compile binaries and make necessary changes in path.
After having the requirements installed, we move to the cracking part. Below this, i am dividing the tutorial into two parts, first we will crack the WPA/WPA2 using MIC aka 4-way handshake. While in second, i'll do cracking using PMKID.
PART A
Let's clear how the MIC cracking actually works. So, in this case, we need a valid 4-way handshake. The handshake consists of many keys that are interchanged during the authentication between the client and access point.
These independent keys are used to generate a common key named 'Message Integrity Code (MIC)'. This generated MIC is used to validate the given password by cracker.
The algorithm to compute MIC is quite long and tricky and i've have covered that up in another tutorial here. So, let the cracking begin.
STEP 1
Conversion to hccapx format
Supposing you already have a captured 4-way handshake using some tool like airodump, but you still need the proper format to supply it to hashcat. To convert it to a proper format (hccapx), you need another tool.
There are already some online services that you may use: https://hashcat.net/cap2hccapx/
But still in case you are wondering to do it locally, clone the hashcat-utils repo from github:
Finally, compile the binaries. After compiling, you will have the binaries under same directory. The binary file that we need is cap2hccapx.bin. To make sure, you have it correctly compiled, try to execute the file, it will throw you back the syntax:
So, after having it installed, use the below given syntax to convert the .cap file to .hccapx hashcat capture format.
So, this will generate a file by the name 'hashfile.hccapx', which is what we are going to use with hashcat. Now, you may move to whatever directory you want, since will be cracking the final format now.
STEP 2
Cracking WPA/WPA2 (handshake) with hashcat
With hashcat, there is a possibily of various attack vectors. We could do a straight dictionary attack, brute-force attack, combinator attack or even masks attack, i.e. making rules to find various possibilities of trying different characters at different positions.
Anyhow, let's study the actual cracking of WPA/WPA2 handshake with hashcat.
Dictionary Attack:

As named, you need a wordlist for it to work. Considering you have solid list of possible wifi passphrases, or if not, you can download the famous ones: https://www.wirelesshack.org/wpa-wpa2-word-list-dictionaries.html
Launch the following command for dictionary attack:
- -a: specifies cracking mode. In our case it's dictionary mode and '/path/to/dict.txt' is complete path to the wordlist.
- -m: hash mode. Specifies what type of hash we are dealing with.
In Case You Receive issues regarding Intel CPU or 'No devices found/left', use --force argument to force the usage of your device.
Brute-Force Attack:
The Brute-force is different than the dictionary attack. Here, we try to replace every character at every possible position in a specified length from a given charset. For example, in a string of length 8, we can try every character from A-Z at every postion in this string.
That's how brute-forcing works and hence very time-consuming. Launch the following command to start your first attempt for brute-forcing:
- -a: specifies the cracking mode and here the value 3 indicates, we are running a brute-force attack.
- ?d?d?d?d?d?d?d?d: is the brute-forcing rule here. It specifies what kind of values to check, where to replace and also assumes how much time could it take to crack the key.
The above mask i.e. '?d?d?d?d?d?d?d?d' states to check a string of length 8 with a digit at every position. You can study about mask attack here: Hashcat Mask Attack.
PART B
Part A was about the handshake cracking. Whilst now, we are going to crack PMKID with hashcat. The PMKID is located in the 1st packet of 4-way handshake and hence it's kind of more useful because we don't need a complete handshake.
The algorithm to compute PMKID is given which is quite easier than that of MIC.
Let the cracking begin for PMKID.
STEP 1
Getting the PMKID hash
The first thing to proceed with PMKID cracking is the pmkid hash. To generate it we need the first packet of the 4-way handshake. Considering you already have that, we will extract the hash from the captured file.
If you are not aware of how to capture the first packet of 4-way handshake, follow this tutorial.
Let's do the conversion. Execute the below command
This will generate a file by the name pmkid.hash that we will use with hashcat to do the cracking.
STEP 2
Cracking WPA/WPA2 (PMKID) with hashcat

So, Cracking WPA/WPA2 has been quite a topic now. In this tutorial, we are going to cover one of the infamous tools 'hashcat' for cracking WPA/WPA2.
Hashcat which is primarily built for brute forcing different kind of hashes using different kind of attack vectors, supports cracking for two of badly known WPA/WPA2 attacks. Well, for the list of available hashes, you can check the hash modes section in the manual:
In previous, you might have seen or even worked with aircrack to crack WPA/WPA2 by capturing a 4-way handshake. But that was not anywhere close to how perfect could this tool be for the purpose. Easefab video converter registration code. Besides, hashcat is a GPU + CPU maintained tool which makes it a lot more faster.
In short, if you own a GPU, always go for hashcat or else you could use an online service or buy out some GPU based server on Internet.
We will cover up with two famous WPA/WPA attacks, precisely the cracking of MIC (4-way handshake) and PMKID (1st packet/handshake). So, let's begin.
Installation
Hashcat is built to work on Windows, Linux and as well as on Mac. You can go to hashcat.net and download the binaries and follow the instruction for your operating system. What we are going to do here is clone a fresh copy of hashcat from github and manually install it on a debain based linux.
Preferably, you should use Kali Or Parrot but a similar distro like Ubuntu will work as well.
Update Your Repo's and install the following dependencies:
Clone hashcat from github and move to directory:
Finally, compile the binaries and we are all set with hashcat.
You may try printing the help manual for hashcat to check whether you have it installed perfectly or not.
Hcxtools:
Now, let's clone and compile hcxtools from github. It is basically a set of various files to convert and generate another version of the supplied input. We will use it to convert the captured traffic into a format understandable by hashcat. Celeste ost golden.
First, clone the repo and move the hcxtools directory:
And finally, run the make command to compile binaries and make necessary changes in path.
After having the requirements installed, we move to the cracking part. Below this, i am dividing the tutorial into two parts, first we will crack the WPA/WPA2 using MIC aka 4-way handshake. While in second, i'll do cracking using PMKID.
PART A
Let's clear how the MIC cracking actually works. So, in this case, we need a valid 4-way handshake. The handshake consists of many keys that are interchanged during the authentication between the client and access point.
These independent keys are used to generate a common key named 'Message Integrity Code (MIC)'. This generated MIC is used to validate the given password by cracker.
The algorithm to compute MIC is quite long and tricky and i've have covered that up in another tutorial here. So, let the cracking begin.
STEP 1
Conversion to hccapx format
Supposing you already have a captured 4-way handshake using some tool like airodump, but you still need the proper format to supply it to hashcat. To convert it to a proper format (hccapx), you need another tool.
There are already some online services that you may use: https://hashcat.net/cap2hccapx/
But still in case you are wondering to do it locally, clone the hashcat-utils repo from github:
Finally, compile the binaries. After compiling, you will have the binaries under same directory. The binary file that we need is cap2hccapx.bin. To make sure, you have it correctly compiled, try to execute the file, it will throw you back the syntax:
So, after having it installed, use the below given syntax to convert the .cap file to .hccapx hashcat capture format.
So, this will generate a file by the name 'hashfile.hccapx', which is what we are going to use with hashcat. Now, you may move to whatever directory you want, since will be cracking the final format now.
STEP 2
Cracking WPA/WPA2 (handshake) with hashcat
With hashcat, there is a possibily of various attack vectors. We could do a straight dictionary attack, brute-force attack, combinator attack or even masks attack, i.e. making rules to find various possibilities of trying different characters at different positions.
Anyhow, let's study the actual cracking of WPA/WPA2 handshake with hashcat.
Dictionary Attack:
As named, you need a wordlist for it to work. Considering you have solid list of possible wifi passphrases, or if not, you can download the famous ones: https://www.wirelesshack.org/wpa-wpa2-word-list-dictionaries.html
Launch the following command for dictionary attack:
- -a: specifies cracking mode. In our case it's dictionary mode and '/path/to/dict.txt' is complete path to the wordlist.
- -m: hash mode. Specifies what type of hash we are dealing with.
In Case You Receive issues regarding Intel CPU or 'No devices found/left', use --force argument to force the usage of your device.
Brute-Force Attack:
The Brute-force is different than the dictionary attack. Here, we try to replace every character at every possible position in a specified length from a given charset. For example, in a string of length 8, we can try every character from A-Z at every postion in this string.
That's how brute-forcing works and hence very time-consuming. Launch the following command to start your first attempt for brute-forcing:
- -a: specifies the cracking mode and here the value 3 indicates, we are running a brute-force attack.
- ?d?d?d?d?d?d?d?d: is the brute-forcing rule here. It specifies what kind of values to check, where to replace and also assumes how much time could it take to crack the key.
The above mask i.e. '?d?d?d?d?d?d?d?d' states to check a string of length 8 with a digit at every position. You can study about mask attack here: Hashcat Mask Attack.
PART B
Part A was about the handshake cracking. Whilst now, we are going to crack PMKID with hashcat. The PMKID is located in the 1st packet of 4-way handshake and hence it's kind of more useful because we don't need a complete handshake.
The algorithm to compute PMKID is given which is quite easier than that of MIC.
Let the cracking begin for PMKID.
STEP 1
Getting the PMKID hash
The first thing to proceed with PMKID cracking is the pmkid hash. To generate it we need the first packet of the 4-way handshake. Considering you already have that, we will extract the hash from the captured file.
If you are not aware of how to capture the first packet of 4-way handshake, follow this tutorial.
Let's do the conversion. Execute the below command
This will generate a file by the name pmkid.hash that we will use with hashcat to do the cracking.
STEP 2
Cracking WPA/WPA2 (PMKID) with hashcat
Just like previous part, we will apply the same rules here except for the hash mode argument. The hash mode value for PMKID cracking is 16800.
Dictionary Attack:
As per syntax we have back in the PART A section for dictionary attack, we will use that very same syntax except for the -m argument which defines what kind of hash we want to crack. We will be cracking pmkid (16800) this time.
While this would crack the key by looping through each line given in the wordlist.
Brute-Force Attack:
We will do same here as last section i.e. providing a mask to crack the hash. This time, just to show how powerful these masks could be, i'll use a different one. So, execute the command for brute-force attack:
The above mask will create combinations of string of length 8 with every alphabet at every possible position. And this sounds like a huge combination that may take a lot of time to complete. To make the attack more faster, we can use the GPU.
Murda beatz drum kit. CPU/GPU
Now, getting into CPU/GPU thing, we just need to know that GPU is a lot more faster than CPU and hashcat have the ability to do cracking on your GPU. Hashcat has following three device modes which can be changed via -d argument:
- 1: CPU which is by default, selected.
- 2: GPU
- 3: DSP, Co-processor.
You can use one of these devices according to what's more suitable for you. For example,
To accomplish PMKID attack on GPU. That's it, i.e. cracking WPA/WPA2 via hashcat.
Conclusion
The conclusion that can be drawn out of all above is that hashcat is not just limited for a number of hashes, infact it's applicable to a wide range of hashes and other possibilities including mixes and concatenated strings. We learned to crack WPA/WPA2 using hashcat.
Besides, hashcat is known of it's power, stability and speed by operating on GPU. It also gives us the possibility of mask attack which let us play with possibilities of testing thousand of thousands strings against the hash.
For Any Questions, Queries, mistakes, you can comment down.
How To Crack WPA/WPA2 With HashCat
The tutorial will illustrate how to install and configure HashCat on a Windows client and crack the captured PMKID or .hccap files using a wordlist dictionary attack.
'Hashcat is the self-proclaimed world's fastest password recovery tool. It had a proprietary code base until 2015, but is now released as free software. Versions are available for Linux, OS X, and Windows and can come in CPU-based or GPU-based variants.'
The WPA2 handshake can be captured on a Linux compatible client like Kali Linux with a supported WiFi card running on VirtualBox. Then converted to the right format depending on the captured method and moved over to the Windows client to be cracked.
Use the guides Capturing WPA2 and Capturing WPA2 PMKID to capture the WPA2 handshake. For this test we will use the famous 'Rockyou' wordlist.
DISCLAIMER: This software/tutorial is for educational purposes only. It should not be used for illegal activity. The author is not responsible for its use or the users action.
Step 1: Download HashCat
Hashcat do not require any installation, it is a portable program it requires you to unpack the downloaded archive.
- First you need to download Hashcat binaries from https://hashcat.net/hashcat/
- Navigate to the location where you saved the downloaded file, and unzip the file
Step 2: Download Wordlist
They are numerous wordlists out on the web, for this test we are going to use the famous 'rockyou'.
- Open the hashcat folder on your harddrive and create a new folder called 'wordlist'
- Download therockyou.txt wordlist from this Link.
- Save the downloaded file in the new folder'wordlist'
Step 3: Prepare Your Captured WPA2 Handshake
Depending on the method you used to capture the handshake you either must format the cap file to 2500 hash-mode or the PMKID file to hashcat 16800 hash-mode .
For how to format the files please see the guides Capturing WPA2 and Capturing WPA2 PMKID.
In this lab we are using a captured PMKID and a pcpa handshake formatted to hashcat readable format. 'HonnyP01.hccapx ' and ' HonnyP02.16800″.
I'm using two different home routers from D-Link and Technicolor for this experiment, both WiFi routers are owed by me.
- The 'HonnyP01.hccapx' file is captured from the D-Link router.
- The ' HonnyP02.16800″ file is captured from the Technicolor router.
Step 4: Start Hashcat
You need to run hashcat in CMD or PowerShell. In this example we will use CMD to execute our commands and crack the handshake.
Open CMD and navigate to the hashcat folder.
Type hashcat64 -h to display all options
Step 5: Crack WPA2
In the First example we will illustrate how to get the password from a converted pcap file '.hccapx'.
Copy your converted file to the hashcat folder, in this example i am copying the file HonnyP01.hccapx to my hashcat folder.
Next we will start hashcat and use the wordlist rockyou, type in the parameters below in CMD.
- hashcat64 the binary
- -m 2500 the format type
- -w 3 workload-profile 3
- HonnyP01.hccapx the formatted file
- 'wordlistrockyou.txt' the path to the wordlist
Best Gpu For Wpa Cracking Free Download
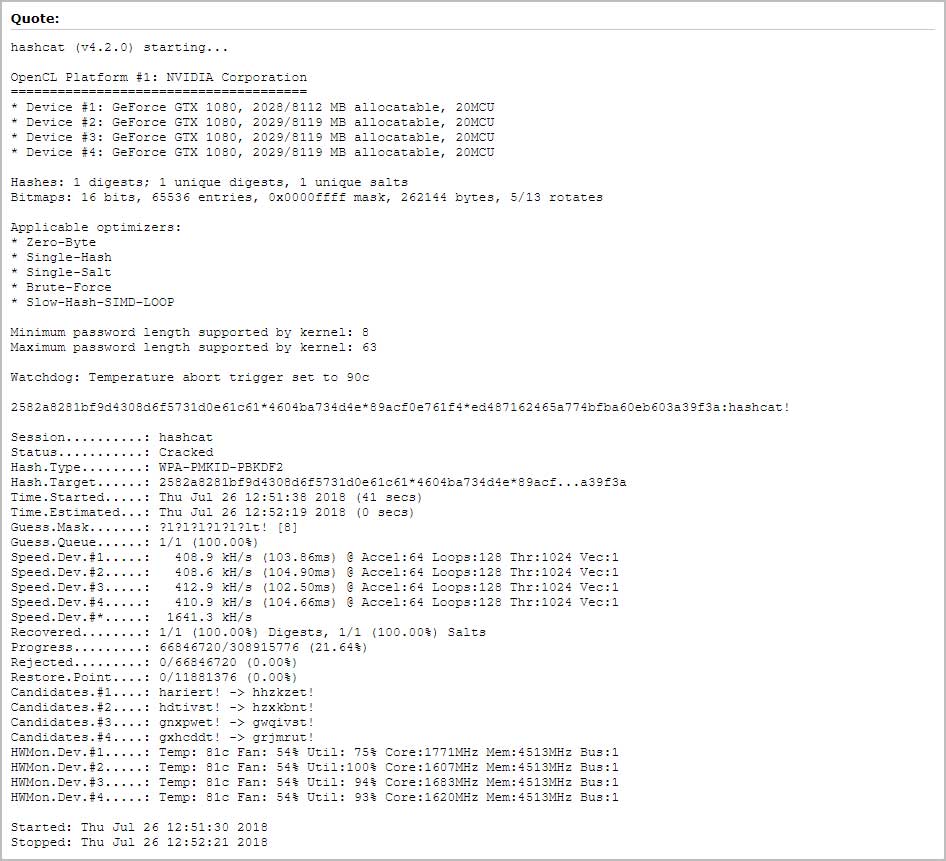
Hashcat will start processing the file, if you are successful the terminal will display the hash and the password.
Here we can see that hashcat was able to match the hash to a password in the wordlist, in this lab the password to the D-Link WiFi is 'password'. You can chose to let the application run trough the wordlist or press 'q' to quit.
Aircrack
You can display the cracked password with the 'show' command or by running the same command again, all cracked hashes will be stored in the 'hashcat.potfile' in the hashcat folder.
To display the cracked password in CDM type the command bellow.
In the next example we will run the same command except now we use the 16800 mode to run the dictionary attack against formatted PMKID file captured from the Technicolor router.
- hashcat64 the binary
- -m 16800 the format type
- -w 3 workload-profile 3
- HonnyP02.16800 the formatted file
- 'wordlistrockyou.txt' the path to the wordlist
Here we can see that the cracked password is 'adsladsl' for the Technicolor router.
Extra: Brute Force Attack And Rule based attack
You can let hashcat brute force the file with the command bellow.
Or use ruled base attack.
Conclusion
Your home or office WiFi can be hacked if you are using a weak password, as always a strong and complex password is still the best defense against an attacker.
Wpa Cracking Software
DISCLAIMER: This software/tutorial is for educational purposes only. It should not be used for illegal activity. The author is not responsible for its use or the users action.
